For the past 20 years web applications have always been the number one action vector for incidents and breaches (DBIR Verizon 2023).
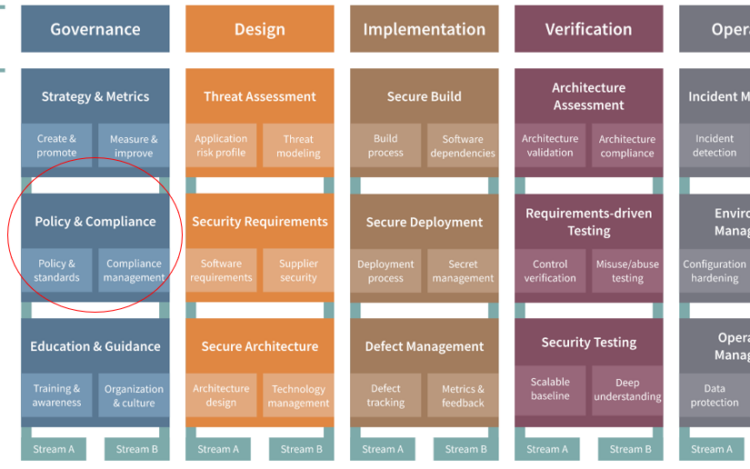
OWASP SAMM offers a systematic approach to tac…
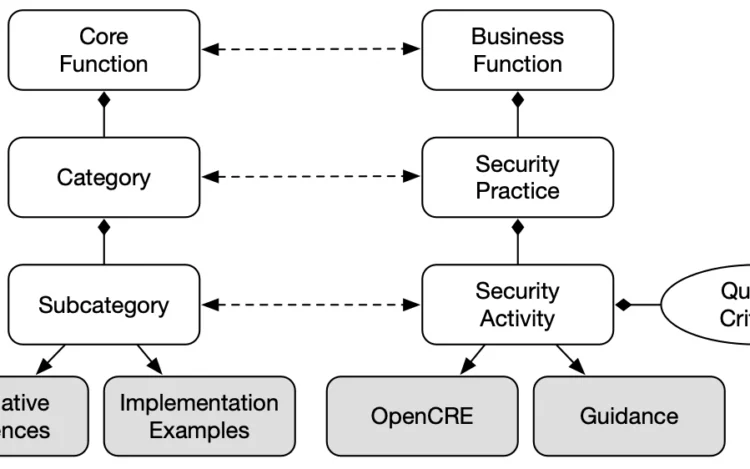
NIST has finalized the Cybersecurity Framework (CSF) 2.0. CSF focuses on understanding, assessing, prioritising, communicating, and above all reducing cybersecurity risks …
In an increasingly digital world, the management and security of our personal information have become critical concerns. Traditional centralized identity management system…
Do you sell any software to any Federal Agency in the US? Then this blog is most definitely of interest to you. Following the memorandum M-22-18, every vendor selling software to US …
Grab your tin-foil hats, dust off your most outdated antivirus software, and get ready to laugh, groan, and maybe even learn a thing or two (what not to do). Let’s dive right i…
Is SOC 2 Worth It?
In this blogpost we will be discussing SOC 2, what are its pros and cons in comparison to the other compliance frameworks available, each with its own strengths and …
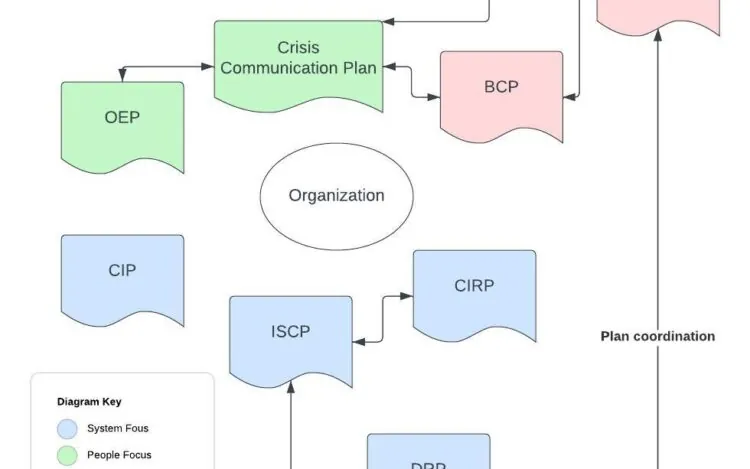
What is a disaster recovery plan?
A disaster recovery plan is your plan for when the dirt hits the fan.
Security pundits like to say things such as “It is not a question of whether your …
Is ISO 27001 worth it?
In this blogpost we will be discussing ISO 27001. What are its pros and cons in comparison to the other general certification and whether or not it is worth the c…
OWASP is the Open Worldwide Application Security Project. It is a non-profit foundation that works to improve the security of software. One of its most recognized contributions …