Updated: 24 September, 2025
24 February, 2025
Have you every been hacked? It sucks right? But don’t worry now, let’s make sure it never happens again.
Welcome to: A Guide on How to Not Get Hacked.
Good news, you’re already taking the first step toward better security awareness. Most cyberattacks don’t happen because hackers are exceptionally skilled. They happen because people make simple mistakes, like using weak passwords, clicking on phishing links, or ignoring software updates. Hackers don’t need to break in when you leave the door wide open.
However, you don’t need to be a cybersecurity expert to protect yourself. By following a few simple but critical security habits, you can drastically reduce the chances of falling victim to cyberattacks. In this guide, we’ll walk you through how to not get hacked, covering practical steps that will keep your data safe and your accounts secure. Because when it comes to cybersecurity, prevention is always better than recovery.
How to not get hacked: 9 key steps
Step 1: Stop Thinking ‘It Won’t Happen to Me’
Hackers don’t just go after big corporations. They love small businesses, startups, and even individuals. Why? Because too many people assume they’re not a target. The first step to not getting hacked is realizing that you are a target. Your data, accounts, and systems are valuable, even if you think they aren’t (there is a price in the black market for them). Remember, in cybersecurity it is not a matter of if you will get hacked, it is a matter of when you will get hacked. Remember, there are 600 million cybersecurity attacks, EVERY DAY.
What to do: Assume you’re a target. Act accordingly.
Step 2: Fortify Your Passwords Like a Medieval Castle
You wouldn’t lock your front door with a paperclip, so why do people still use password123? Weak passwords are the easiest way to get hacked. Attackers use automated tools to brute-force their way in.
What to do:
- Use a password manager to generate and store strong passwords.
- Enable multi-factor authentication (MFA), your second line of defense.
- Never reuse passwords across sites. If you are using a password manager this is not even necessary as you only need to remember one password.
Step 3: Update Everything, All the Time
Hackers aren’t always breaking in, they’re often just walking through open doors left unlocked. Software vulnerabilities are their best friends, and outdated software is a goldmine of weaknesses.
What to do:
- Enable automatic updates on everything, your OS, apps, routers, IoT devices.
- Don’t ignore those “Update Now” notifications. They exist for a reason.
Step 4: Be Suspicious of Everything (Yes, Everything)
If something seems off, it probably is. That urgent email from your bank? A scam. The random attachment from HR? Likely malware. Social engineering is the hacker’s favorite technique.
What to do:
- Never click links or download attachments from unknown sources.
- Verify requests for sensitive info. Call the person directly or contact them through another medium.
- If an email feels urgent or threatening, it’s probably phishing.
Step 5: Secure Your Wi-Fi Like Your Wallet
If your home Wi-Fi password is still admin or 12345678, you’re practically inviting hackers in. Public Wi-Fi? Even worse. Hackers love unsecured networks for sniffing traffic and stealing credentials.
What to do:
- Change your router’s default password.
- Use WPA3 encryption if available.
Step 6: Backup, Because Bad Things Happen
Ransomware doesn’t care about your files. If you get hit and don’t have backups, you might as well wave your data goodbye (or your money, as you will need to pay to get it back).
What to do:
- Set up automatic backups (cloud + offline).
- Follow the 3-2-1 rule: 3 copies, 2 locations, 1 offline.
- Test your backups, don’t assume they work until you restore one.
Step 7: Minimize Your Digital Footprint
The more information hackers can find about you, the easier their job becomes. That Facebook quiz that asks for your first pet’s name? It’s mining your security question answers.
What to do:
- Share less personal information online.
- Review your privacy settings on social media.
- Regularly check what personal data is publicly available.
Step 8: Educate Yourself and Your Team
Security isn’t just about tools, it’s about people. One weak link (e.g. an employee clicking a phishing link) can compromise your entire organization.
What to do:
- Train yourself and your team on cybersecurity best practices.
- Conduct phishing tests to see who falls for scams.
- Make security awareness an ongoing effort, not a one-time event.
Step 9: Accept That Security is Never ‘Done’
Cybersecurity isn’t a checklist, it’s a mindset. Attackers evolve. Threats change. The only way to stay safe is to continuously adapt.
What to do:
- Regularly review your security posture.
- Stay informed on emerging threats.
- Adopt a zero-trust mindset, assume everything needs verification.
Final Thoughts
If you follow these steps, will you be 100% hack-proof? No. But you’ll be significantly harder to hack than the majority of people and companies out there. Hackers are opportunists, they go for easy targets. Make sure you’re not one of them.
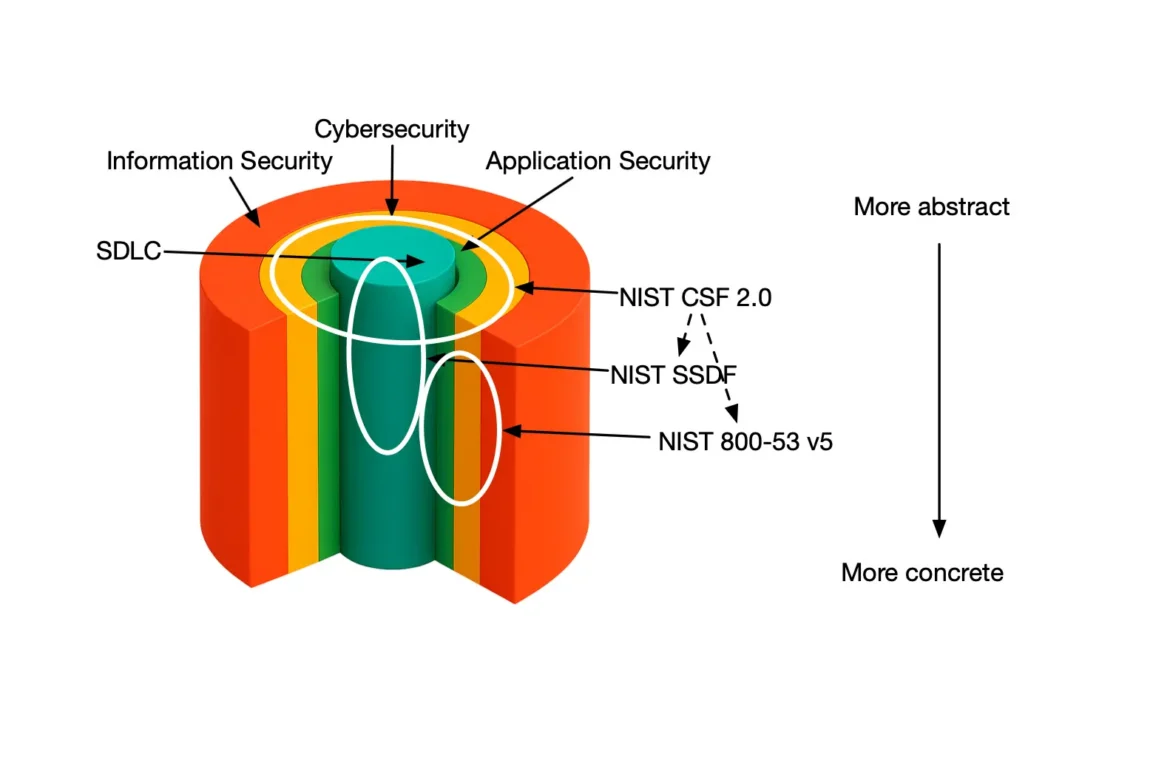
Want to take your security even further? Start by assessing your security maturity with OWASP SAMM and other industry best practices using SAMMY. Because the best way to not get hacked… is to be prepared. And in case things ever do go south, having a solid contingency plan in place will make all the difference.