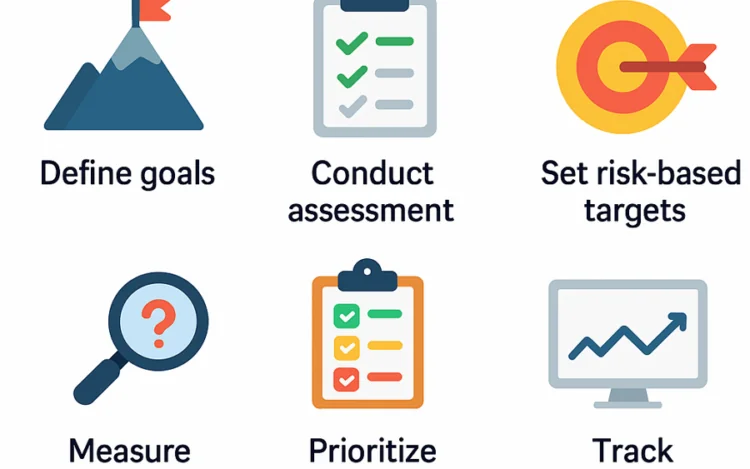
Understanding OWASP SAMM is only the beginning. The real value comes from using it to […]
The U.S. cybersecurity strategy seems to be lightyears ahead of the EU. I strongly believe[…]
Cybersecurity in general and application security (AppSec) in particular are extremely challenging topics. They run[…]
Application security requires a systematic approach and requires dealing with software security throughout every stage[…]
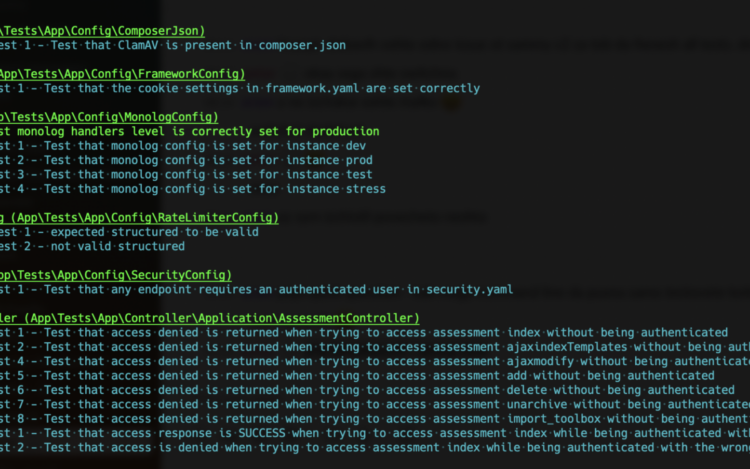
Security verification is about validating that a system or application adheres to predefined security requirements[…]
Codific is proud to receive the renewal of the ISO 27001 audit certification. ISO 27001[…]
Ever heard the saying “our team is our greatest asset”. I’d dare to say that[…]