Updated: 9 March, 2026
9 June, 2022
Ever heard the saying “our team is our greatest asset”. I’d dare to say that this is rule number 1 through 10 if you are running a company. Any company! Well, except for a one-man show (where this is self-explanatory and you don’t really need a rule)!
Thus security training and organizational culture are the pillars of your SDLC programme. Unless you are just trying to check the boxes this security practice should get the highest priority in your SAMM implementation roadmap.
In this blog series, we present how Codific implements OWASP SAMM. In each blog we focus on a specific security practice and highlight the processes and tools we use to achieve a certain maturity level. If you would like to learn more about OWASP SAMM, take our free SAMM training.
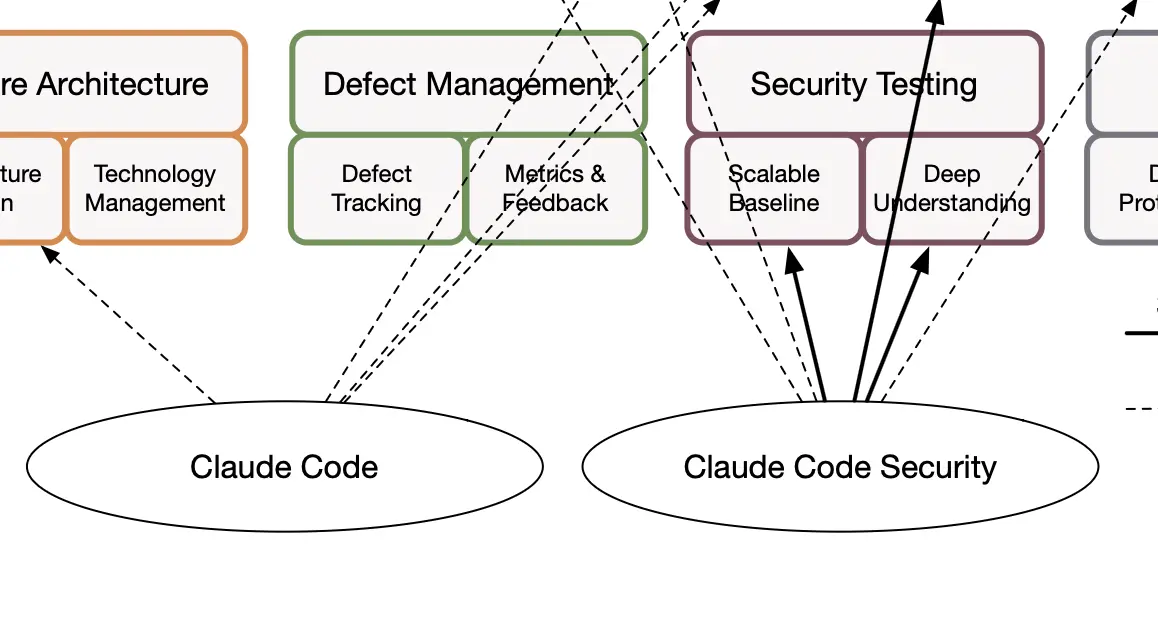
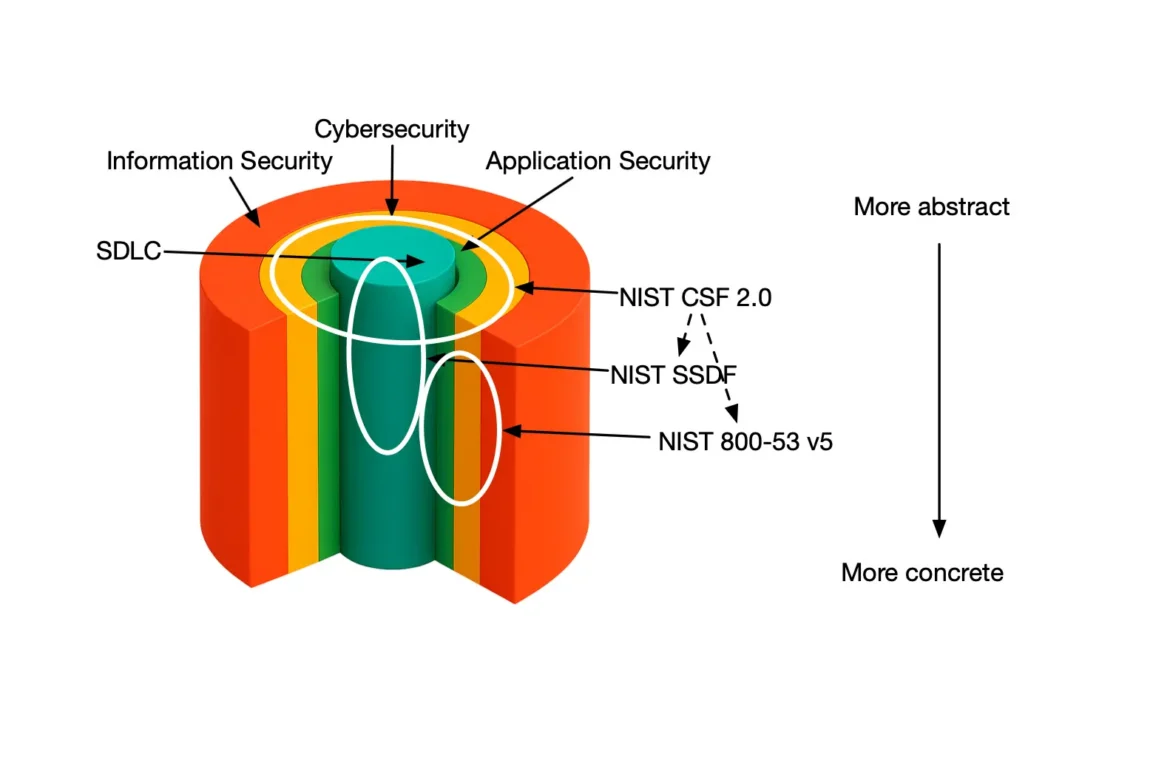
My journey in application security (AppSec) started almost 20 years ago at the Imec-DistriNet research lab of the University of Leuven. Back in the days secure software development was more of a hobby driven by a handful of enthusiasts. AppSec took its place under the spotlight with the release of Microsoft Security Development Lifecycle and the efforts from the OWASP community. Today cybersecurity is the buzzword train everybody tries to jump in. There are currently over 100 active OWASP projects that include code, software, reference material, documentation, tools and community all working to secure the world’s software. One of these projects is the Software Assurance Maturity Model (SAMM). SAMM is a structured approach to help your organization formulate and implement a tailored SDLC programme.
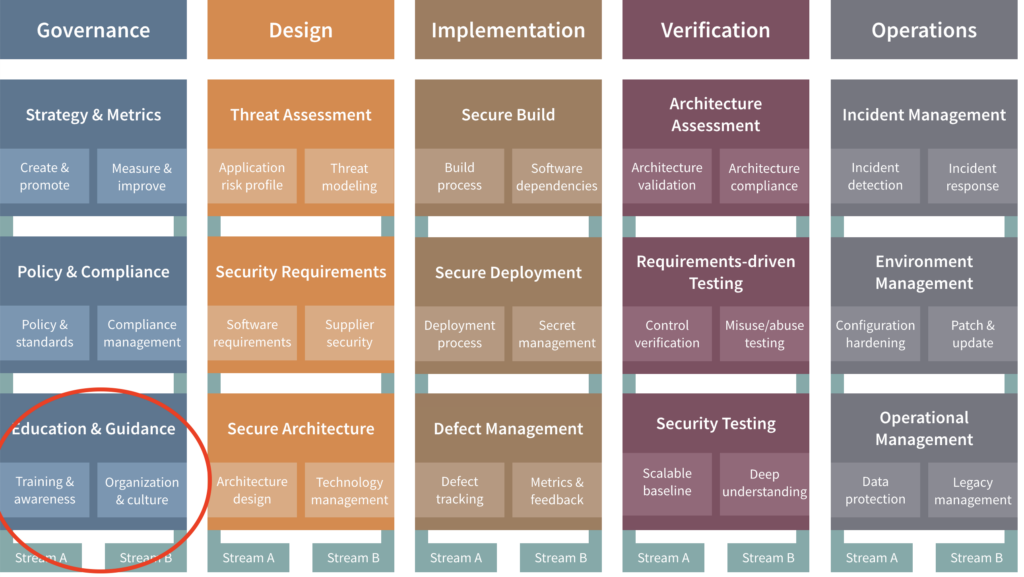
Implementing SAMM Education and Guidance
In this blog, I will present a number of selected best practices we have implemented at Codific. The Education and Guidance practice focuses on providing personnel involved in the software lifecycle with knowledge and resources to design, develop and deploy secure software. A major theme in delivering secure software is providing training for employees and increasing security awareness. In addition to training, organizations need to make an investment in improving its culture to promote application security through collaboration between teams.
At Codific we have selected a set of mandatory and optional security trainings. These are available to everyone involved with software development lifecycle. We have security champions available to each product team. Our security champions are required (and eager) to follow a more extensive training with 3rd party certifications. We’ve also set up an informal secure software center of excellence. Amongst their responsibilities falls an in-house cross team training program to make sure security is the responsibility of all of our colleagues and not just the InfoSec team.
Extract from the OWASP SAMM Fundamentals course
Security Trainings
All our colleagues involved in software development lifecycle are required to take a number of trainings during their onboarding. Our InfoSec team updates the trainings on a yearly basis. Currently the set of mandatory courses include:
- Web Security Fundamentals by an ex-colleague of mine from DistriNet Philippe De Ryck
- OWASP Top 10 Overview by Jim Manico
- Web Security and the OWASP Top 10 by Troy Hunt
Security Champion Programme
AppSec is a really cool topic and no wonder most of our colleagues are really enthusiastic about “hacking stuff”. Our current security champion programme includes a number of certified trainings from Offensive Security. A true security champion is much more likely to find his own “drugs” (such as HackTheBox and TryHackMe).
All our security champions are also part of the dev team so the security knowledge flows naturally into the projects. Codific’s internal pen-tests are conducted by the security champions. To avoid any potential bias we always make sure pen-tests are performed by pen-testers who are not working on the given project.
Extract from the OWASP SAMM Fundamentals course
The Culture of Pervasive Security
Despite being a fully remote firm, we do get together every 2-3 months for a week to socialize and share some experiences. Obviously, part of the sharing includes the “Codific Top 10”, which is curated content from both internal and external pen tests. Although this information is already pushed in all affected products it makes sense to harden the knowledge in order to avoid similar mistakes in the future.
Internal Capture-the-Flag Events
Occasionally, we also organize capture-the-flag like internal competitions. They are so much fun and actually require very little preparation. OWASP Juice Shop is a recommended place to start. If you run the CTF as an actual competition with prizes you do need to make sure the team cannot access any solutions on the web.
Extract from the OWASP SAMM Fundamentals course
Summary
In this blog we have presented how Codific implements the Education and Guidance practice. We believe this is the starting point for your SDLC programme whatever your organization’s size or vertical. A culture of pervasive security is also likely to reduce any friction you might encounter throughout introducing SAMM to your organization. We have shared a list of trainings, presentations and events you could easily introduce for your organization. Note that this practice is also much easier to schedule in terms of budget and planning.
What do we build with SAMM and SAMMY?
Codific is a team of security software engineers that leverage privacy by design principles to build secure cloud solutions. We build applications in different verticals such as HR-tech, Ed-Tech and Med-Tech. Secure collaboration and secure sharing are at the core of our solutions.
Videolab is used by top universities, academies and hospitals to put the care in healthcare. Communication skills, empathy and other soft skills are trained by sharing patient interviews recordings for feedback.
SARA is used by top HR-Consultants to deliver team assessments, psychometric tests, 360 degree feedback, cultural analysis and other analytical HR tools.
SAMMY Is a Software Assurance Maturity Model management tool. It enables companies formulate and implement a security assurance program tuned to the risks they are facing. That way other companies can help us build a simple and safe digital future. Obviously our AppSec program and SAMMY itself is built on top of it.
Attendance Radar is the easiest way to track attendance in higher education. It automatically registers students that are in the room.
We believe in collaboration and open innovation, we would love to hear about your projects an see how we can contribute in developing secure software and privacy by design architecture. Contact us.
Official resources