The Digital Operational Resilience Act (DORA), officially known as Regulation (EU) 2022/2554, represents a shift […]
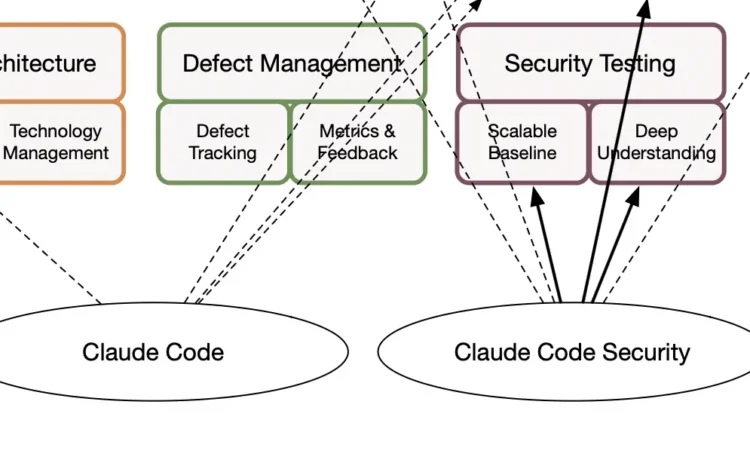
Everyone can now write code with Claude and get to production in a weekend. So[…]
Security programs rarely fail because teams do not care. They fail because the work gets[…]
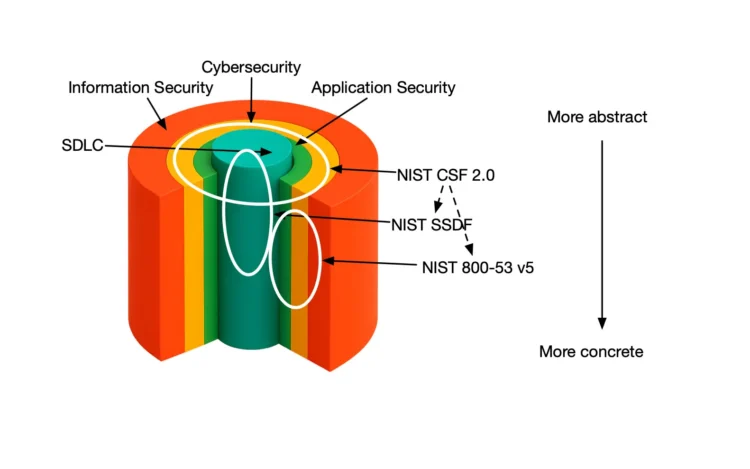
For the past couple of decades, organizations have increasingly invested in security. Unfortunately, they often[…]
If you build or look after web applications, you have probably bumped into the OWASP[…]
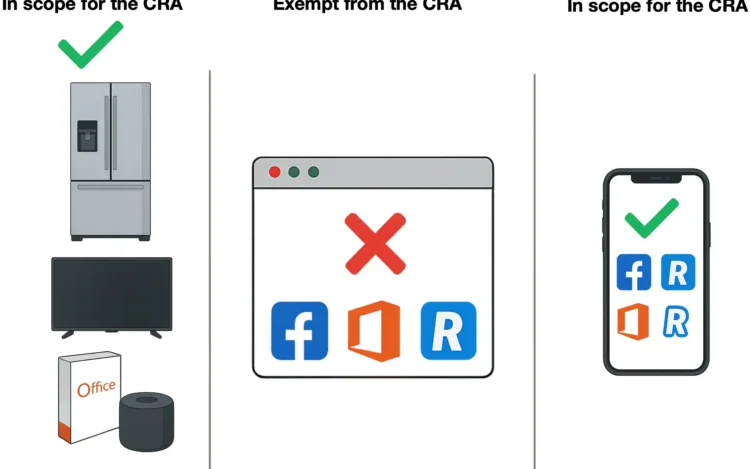
The upcoming Cyber Resilience Act (CRA) is a EU regulation that was published on November[…]
The warning shots are over. The NIS 2 Directive is live, and enforcement has begun.[…]
As software systems grow more complex, proving that they are secure has become as important[…]
Most organizations conduct security assessments, yet few turn them into meaningful improvement. Traditional cybersecurity gap[…]
Many organizations treat Common Vulnerabilities and Exposures (CVEs) as first-class citizens. Some even enforce strict[…]
Application security (AppSec) remains one of the toughest challenges modern organizations are facing. Despite heavy[…]
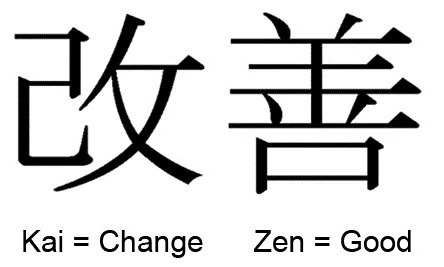
By embracing the Japanese Kaizen philosophy of continuous incremental improvement, your AppSec program can evolve[…]