Updated: 9 March, 2026
28 March, 2023
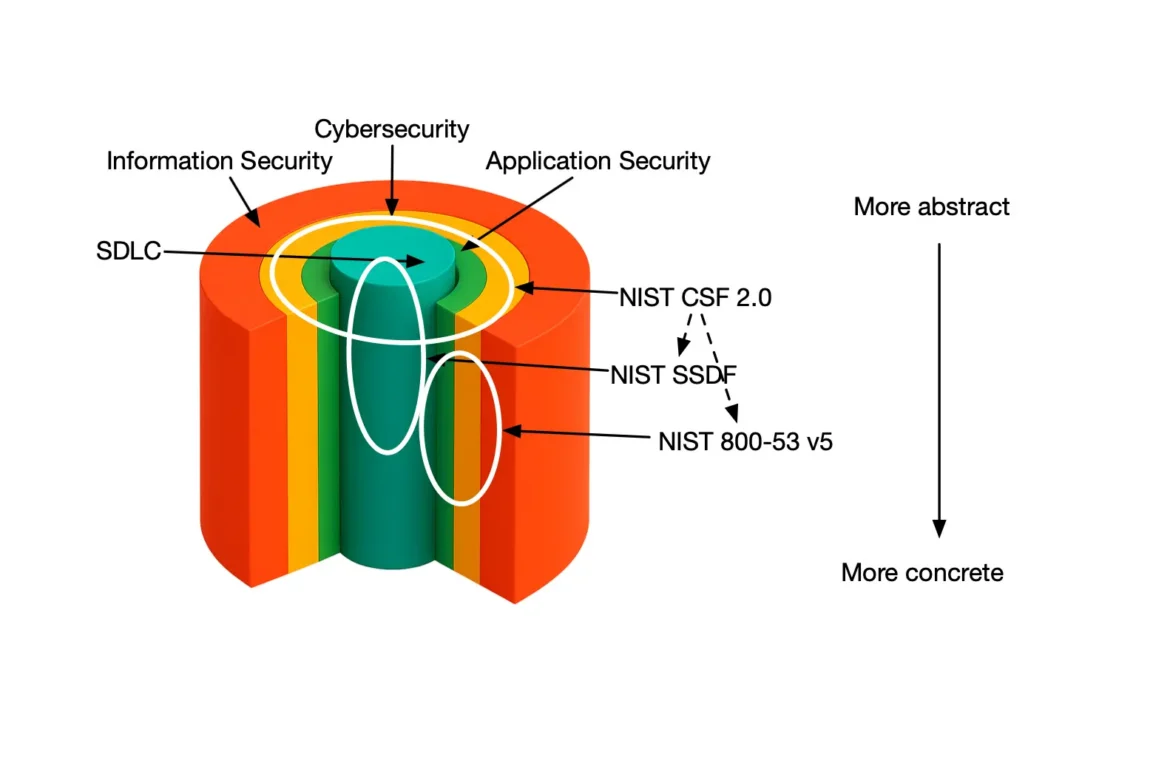
Software security is now a number one risk worldwide. It is literally on the US president’s agenda who has recently announced the national cybersecurity strategy. Data breaches are regular events. Even the most security-aware firms out there are struggling to tackle the application security (AppSec) challenge. Let alone the scale-ups with a limited expertise in the domain of software security do not even stand the chance. Yet software security is not a rocket science. It is a well-defined problem with an overwhelming amount of resources easy to tap into. With OWASP SAMM there is also a clearly defined methodology on how to create an improvement roadmap. One of the many questions that remains open though is how much should an organization spend on software security.
In this blog I look into the cost of introducing application security at a scale-up.
Key takeaways
- Leverage OWASP SAMM as an application security programme.
- The highest ROI security activities in an organization are: threat modeling, education and effective security testing.
- As a rule of thumb, invest 10% of everyone’s time in security.
Why software companies struggle with software security?
It is ironic that many of the data breaches in retrospect could have been (easily) prevented by leveraging the body of knowledge within the OWASP community and projects. One of the factors in the current realities is that security always gets limited budget, hence limited attention. That is all but a surprise. Security is rarely used as an essential added value to the software product. Organizations often confider software security a pain rather than an opportunity. Factors, such as reputation damage as well as regulatory pressures provide a clear motivation to become at least as good as your peers. However, the main contributing factor to the software security realities is the inefficient security budget spending.
The OWASP community provides lots of resources, best practices and tools to help any company build an effective AppSec programme. However all of that is overwhelming, especially from a scale-up perspective. There is a lot of noise in terms of the most efficient security practices and it is unclear where to start. Adding security tooling is the obvious low hanging fruit, but does not always bring the best return on investment. In fact, it might even be counterproductive and overwhelm the security teams literally with noise.
What is a good starting point to introduce software security in my organization?
I have over 15 years of academic and industry experience in software security. I am also actively involved in managing the AppSec programme in a scale-up as well as a Fortune 500 organization. Here are my top 4 recommendations when it comes to the definition of your AppSec roadmap.
Create an application security programme using OWASP SAMM
Start with OWASP SAMM. SAMM is a full-blown AppSec management program and it is the table of contents for nearly the complete body of knowledge within the OWASP community.
Invest in training and awareness
Educate everyone as the tool with a fool is still a tool (this is not a typo).
- Introduce a mandatory general software security training track for everyone in your team. This training should at least include a training on OWASP Top 10, security design principles, web application security fundamentals. For a full list I refer to one of my earlier blogs.
- Ideally everyone, but at least your test engineering team member(s) should get an additional training on OWASP Application Security Verification Standard and the Mobile Application Security Verification Standard.
- Finally, do select security champion(s) and teach subscribe them for a certified pen tester course track.
Threat modeling has the highest ROI
Threat model to explicitly focus on risk, rather than the useless CVSS impact scores. People often associate threat modeling a military-like exercise where every participant is a “black belt” hacker. They could not be more wrong. Everyone can threat model. The more you do it the better you’ll get. In a nutshell, threat modeling is a brainstorming session where the stakeholders sync on risks, threats and countermeasures. After a couple of runs threat modeling should be as easy and fun as going for lunch together with the team.
Focus on effective security testing
Start from another great OWASP project, namely ASVS. We recommend leveraging ASVS as a security requirements framework. You don’t have to implement it in its entirety. In line with best practices in software engineering make sure that your QA teams test your applications against ASVS (or its subset). Furthermore, invest in unit tests based on ASVS that you run as a regression suite in your CI/CD. Finally, introduce periodic pen tests that focus on risk and creating issues, rather than spitting out a 100 page PDF report.
How much does a decent software security programme cost to my company?
The short answer is roughly 12% of your yearly manpower time for year 1. After that probably less, but once you get the taste of being a champion you are likely to want to keep it up. I cannot provide a quantitative measurement for your return on investment. Qualitatively though, you will have taught your team “to fish, instead of bringing them the fish”.
Here are the rough estimates for a technical team of 6 engineers. Let’s call one of these engineers to be your AppSec senior manager / security champion, one of them would be a purple team member in charge of pen testing and one of them would be in charge of testing and verification.
| Type of work | Description | Total person-days per year |
|---|---|---|
| Management | Your AppSec manager will need about half a day per week for managing SAMM | 22 |
| Education | ||
| Your engineering team will need about 80 hours to watch the basic security curriculum trainings | 60 | |
| Your full team should take an in-depth 2-day Threat Modeling training | 12 | |
| Your testing engineer(s) would need about a week to familiarize themselves with OWASP ASVS | 5 | |
| Your purple team member(s) would roughly need 2 person-months to get a decent pen testing training | 40 | |
| Security activities | ||
| Lets assume your full team will participate in a bi-monthly 2-hour threat modeling session for at least one of your software products | 9 | |
| Pen testing by your purple team that takes roughly a week and let’s run that twice a year | 10 | |
| Decent ASVS-based regression tests by your test engineer(s) should take about 20 days | 20 | |
| Total person-days for a 6-member team: | 178 |
For a team of 6 that comes down to roughly 9% of your team’s total workforce time.
While my calculations reflect only on team members involved in the SDLC it is essential to include everyone else in the AppSec education and training programme. That would dilute the numbers presented here and lower your total security budget requirements.
What about SBOM and other DevSecOps tools?
In a mature AppSec programme tools are absolutely critical to improve productivity. Unfortunately throwing the tools at the application security problem is not going to magically solve it. It might even make the situation worse if you don’t have an Application Security programme in place. I strongly believe that once your AppSec programme is up-and-running adding all of these tools is a matter of hours to plug them in and make them work for you.
Conclusion
Software security is a critical aspect of business operations. Organizations, particularly scale-ups, must prioritize application security in order to protect their data and systems. While there is no one-size-fits-all approach to software security investment, organizations should consider implementing OWASP SAMM as a framework and allocating 10% of their resources to security initiatives. In my opinion threat modeling, security training, and effective security testing yield the highest return on investment. By investing in software security, organizations can safeguard their operations, maintain customer trust, and avoid the substantial costs associated with data breaches and reputational damage.