Have you every been hacked? It sucks right? But don’t worry now, let’s make sure […]
Fraud against government programs costs taxpayers billions of dollars every year, threatening the integrity of[…]
In today’s digital landscape, cybercrime is escalating at an alarming rate, with projected damages reaching[…]
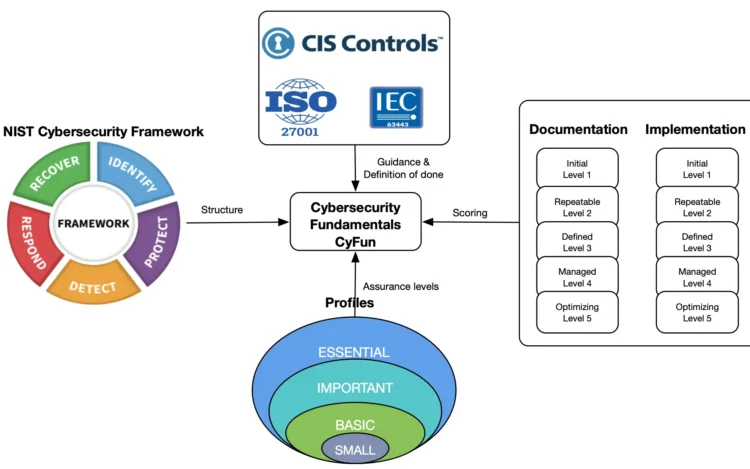
Introduction In this blog, we will focus on helping you understand what is Cybersecurity Fundamentals[…]
Dear disgruntled employee (let’s call you Mallory): Tired of working long hours with no holidays,[…]
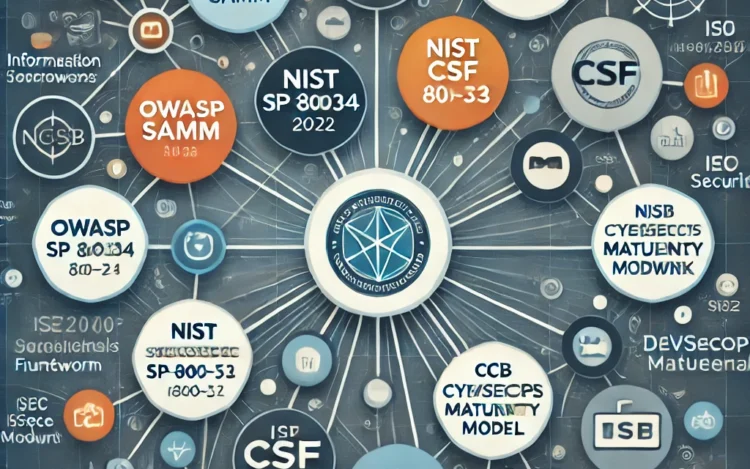
Navigating the complexities of cybersecurity frameworks can be challenging, but understanding how to implement NIST[…]
In the evolving landscape of cybersecurity, organizations face the challenge of protecting their systems and[…]
HIPAA, the Health Insurance Portability and Accountability Act of 1996, is a critical federal law[…]
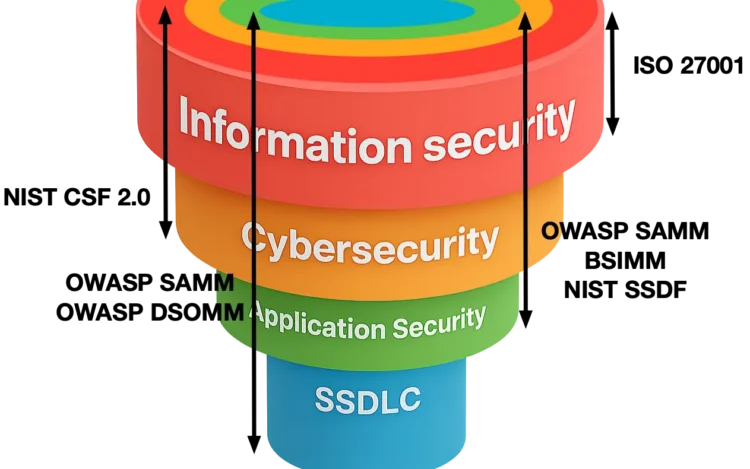
The terms information security and cybersecurity are often used interchangeably, which frequently leads to confusion.[…]
The U.S. cybersecurity strategy seems to be lightyears ahead of the EU. I strongly believe[…]
Application security is a complex discipline. To make things even harder for us, it is[…]
What is FISMA and why is it important? The Federal Information Security Modernization Act (FISMA)[…]