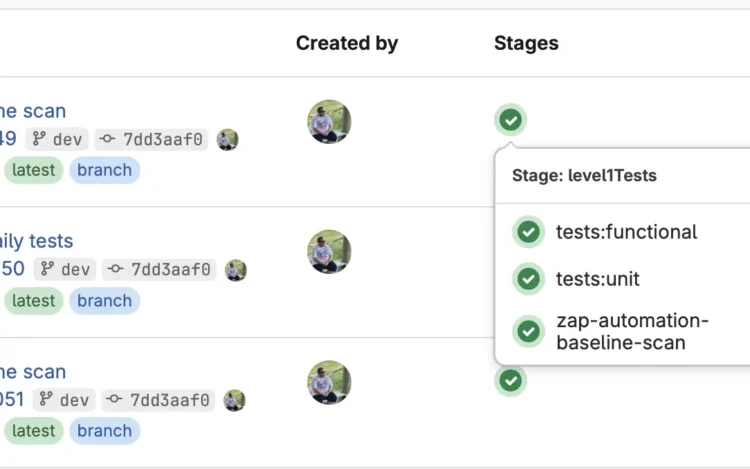
In this technical article, we will explore how to improve your DevSecOps processes by integrating […]
Most security issues in software stem from one simple problem: teams try to fix them[…]
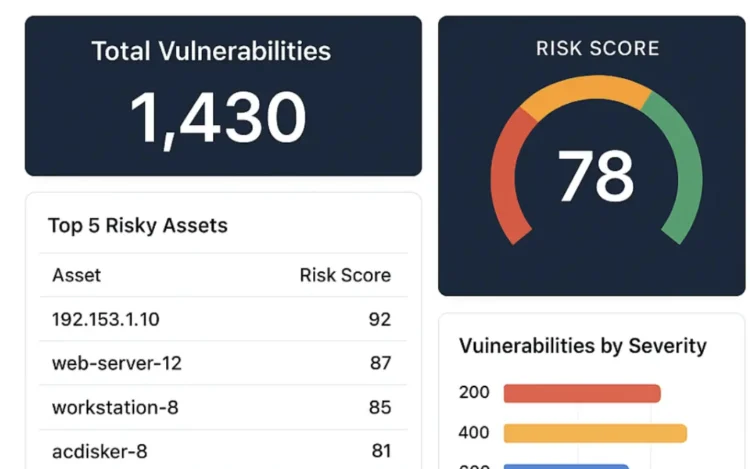
You’ve probably heard the saying, “You can’t manage what you don’t measure.” If you are[…]
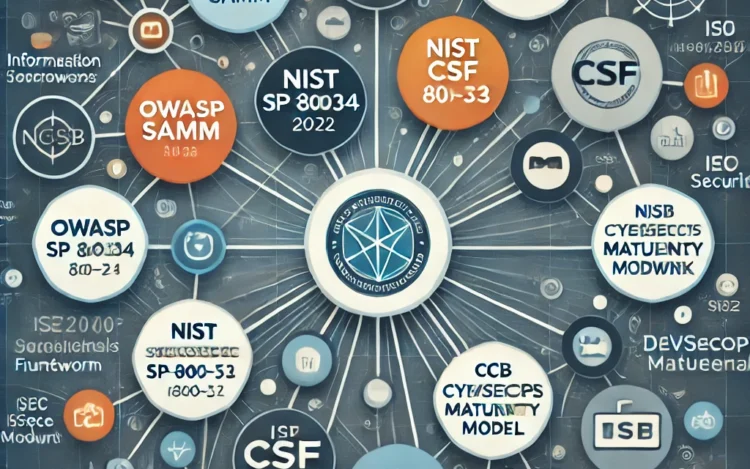
Official framework, regulation and standard pages mentioned in this article CRA GDPR OWASP SAMM[…]
Modern software development moves fast, and so do the security challenges that come with it.[…]
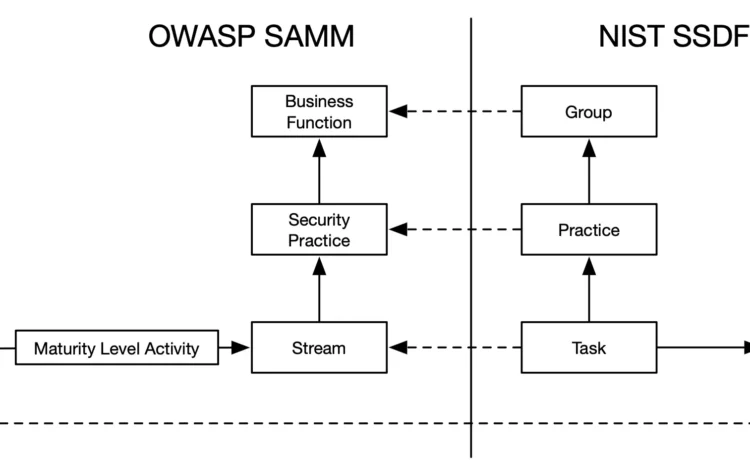
Understanding OWASP SAMM is only the beginning. The real value comes from using it to[…]
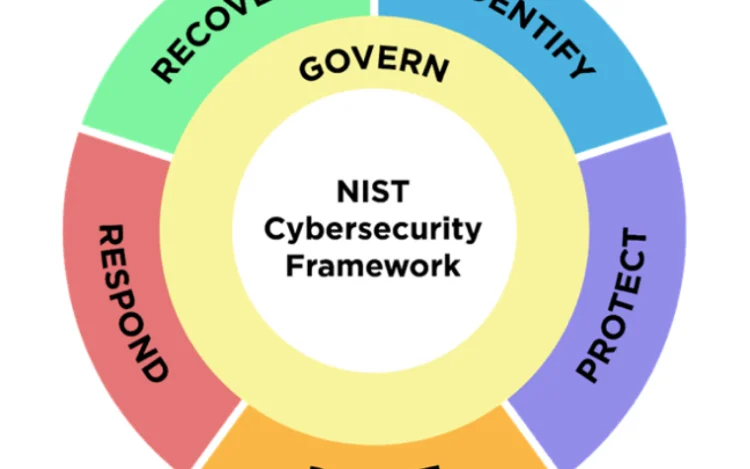
The U.S. cybersecurity strategy seems to be lightyears ahead of the EU. I strongly believe[…]
Application security is a complex discipline. To make things even harder for us, it is[…]
Over the past year, our SAMMY tool has grown significantly. It now supports not just[…]
What is FISMA and why is it important? The Federal Information Security Modernization Act (FISMA)[…]
Managing cybersecurity risks requires a clear strategy combining people, processes, tools, and knowledge, all guided[…]
OWASP Software Assurance Maturity Model (SAMM) is one of the only comprehensive frameworks available for[…]