Is ISO 27001 worth it? In this blogpost we will be discussing ISO 27001. What […]
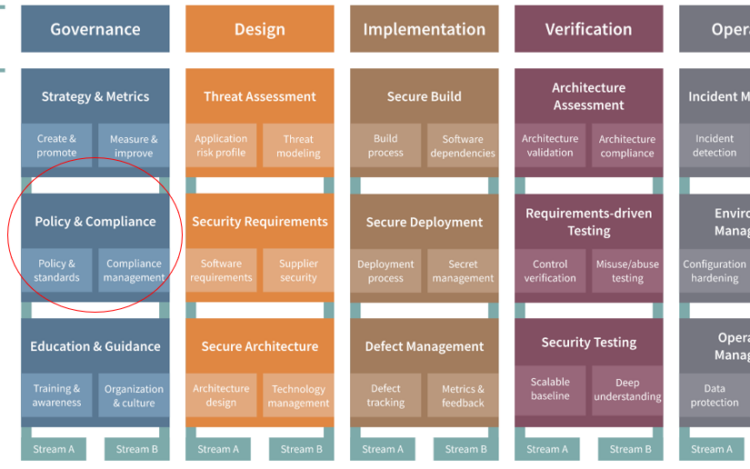
OWASP is the Open Worldwide Application Security Project. It is a non-profit foundation that works[…]
Software Backups Reasons to back up your software seem pretty obvious, however as it can[…]
Software security is now a number one risk worldwide. It is literally on the US[…]
In the dynamic digital realm, security is not a luxury, it is an imperative. As[…]
A Fun Way to Enhance Team Building Key Takeaways: CTF games offer a dynamic platform[…]
Have you ever wondered about the initial steps to ensure data privacy? Do you ever[...]
In the era of data-driven innovation, software development plays a critical role in managing sensitive[…]
Application security has been a hot topic for decades. It was a buzzword in 2001,[...]