Everyone can now write code with Claude and get to production in a weekend. So […]
For the past couple of decades, organizations have increasingly invested in security. Unfortunately, they often[…]
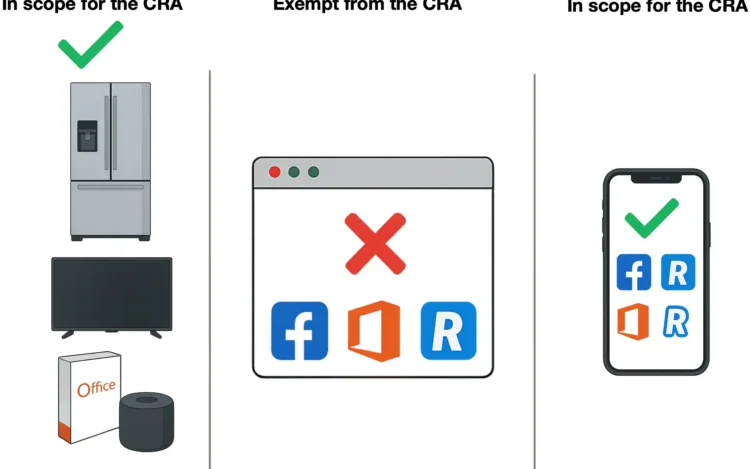
The upcoming Cyber Resilience Act (CRA) is a EU regulation that was published on November[…]
As software systems grow more complex, proving that they are secure has become as important[…]
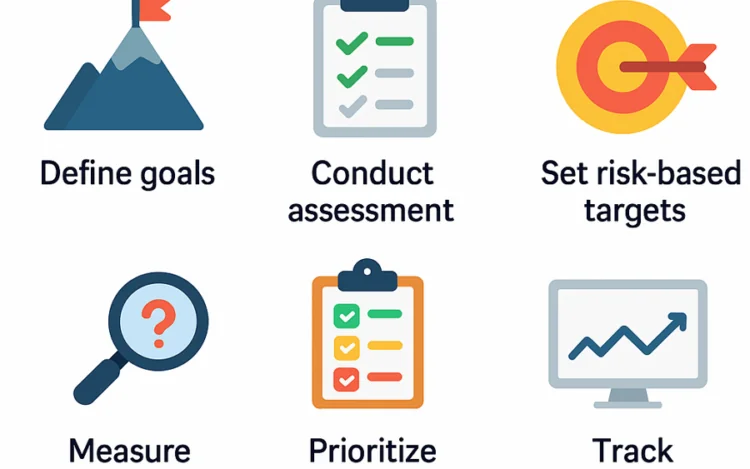
Most organizations conduct security assessments, yet few turn them into meaningful improvement. Traditional cybersecurity gap[…]
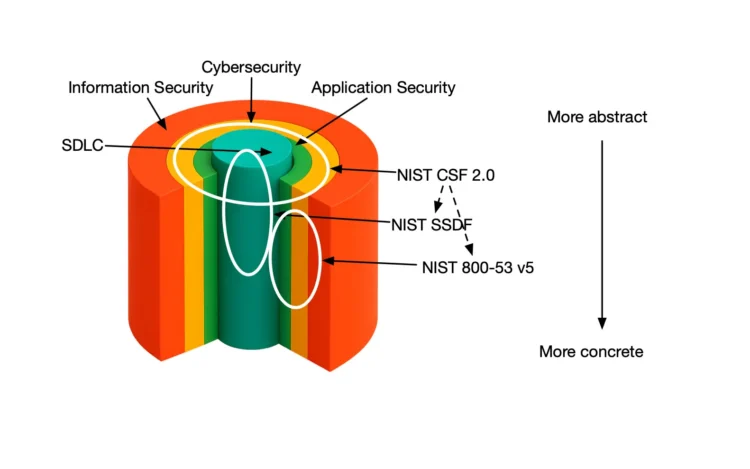
Application security (AppSec) remains one of the toughest challenges modern organizations are facing. Despite heavy[…]
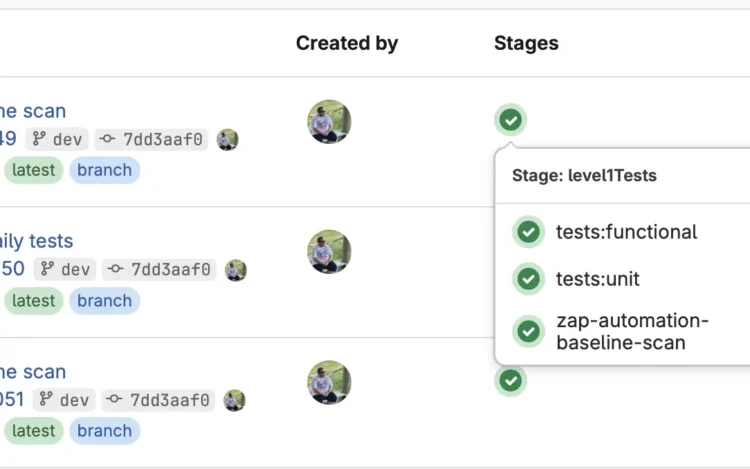
Your DevSecOps pipeline is fast, automated, and built to scale. But is security truly integrated,[…]
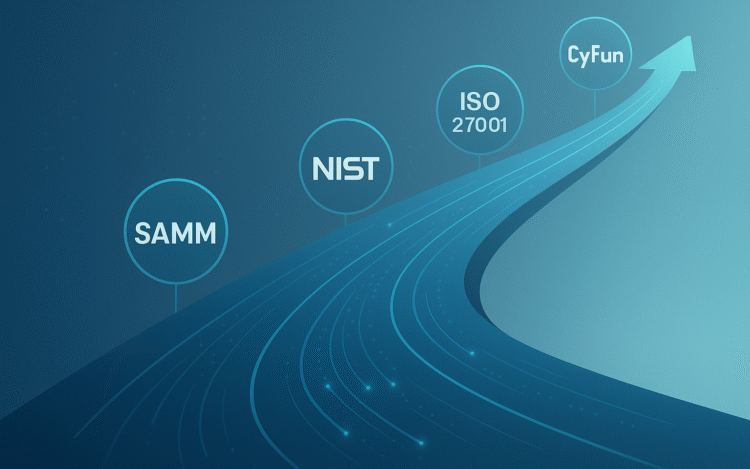
About 4 years ago I have joined the OWASP Software Assurance Maturity Model (SAMM) project[…]
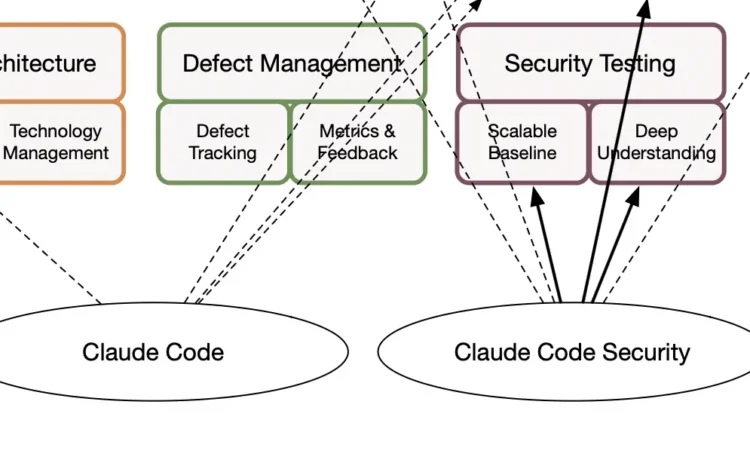
In this technical article, we will explore how to improve your DevSecOps processes by integrating[…]
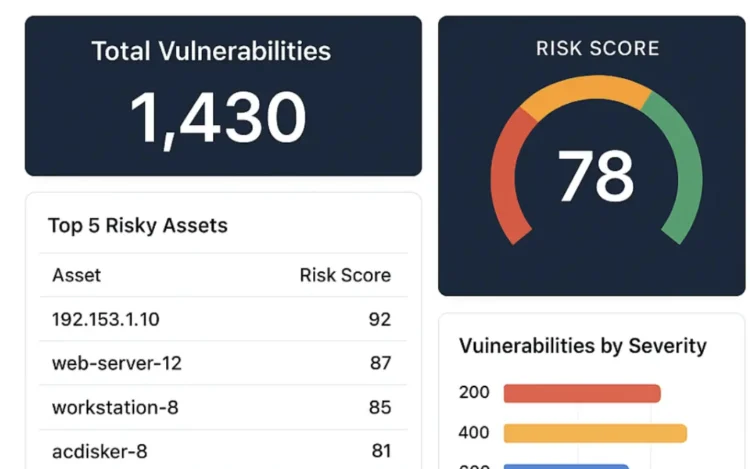
You’ve probably heard the saying, “You can’t manage what you don’t measure.” If you are[…]
Modern software development moves fast, and so do the security challenges that come with it.[…]
Understanding OWASP SAMM is only the beginning. The real value comes from using it to[…]