24 March, 2026
The Digital Operational Resilience Act (DORA), officially known as Regulation (EU) 2022/2554, represents a shift in how the European Union’s financial sector manages technology. By consolidating fragmented national rules into a single, cohesive framework, DORA ensures that all financial entities—from global banks to local credit rating agencies—can withstand, respond to, and recover from ICT-related disruptions.
This summary provides a deep dive into the legislative pillars of DORA, optimized for those looking to understand the core requirements of this digital-first regulatory landscape. For the full regulation refer to the EUR-lex website.
If you are interested in resources on European regulations we also have a website dedicated to the best EU CRA resources.
Scope: Who Does DORA Apply To?
DORA has an impressively broad reach, covering 20 distinct categories of financial entities. These include:
- Credit institutions and payment institutions.
- Investment firms and crypto-asset service providers.
- Central securities depositories and central counterparties.
- Insurance and reinsurance undertakings.
- ICT third-party service providers, including cloud giants.
Exemptions and Proportionality
DORA isn’t a “one-size-fits-all” hammer. It explicitly excludes small institutions like microenterprise insurance intermediaries and certain pension schemes with fewer than 15 members. Furthermore, the Principle of Proportionality is woven into the text: entities implement rules based on their size, risk profile, and the complexity of their operations.
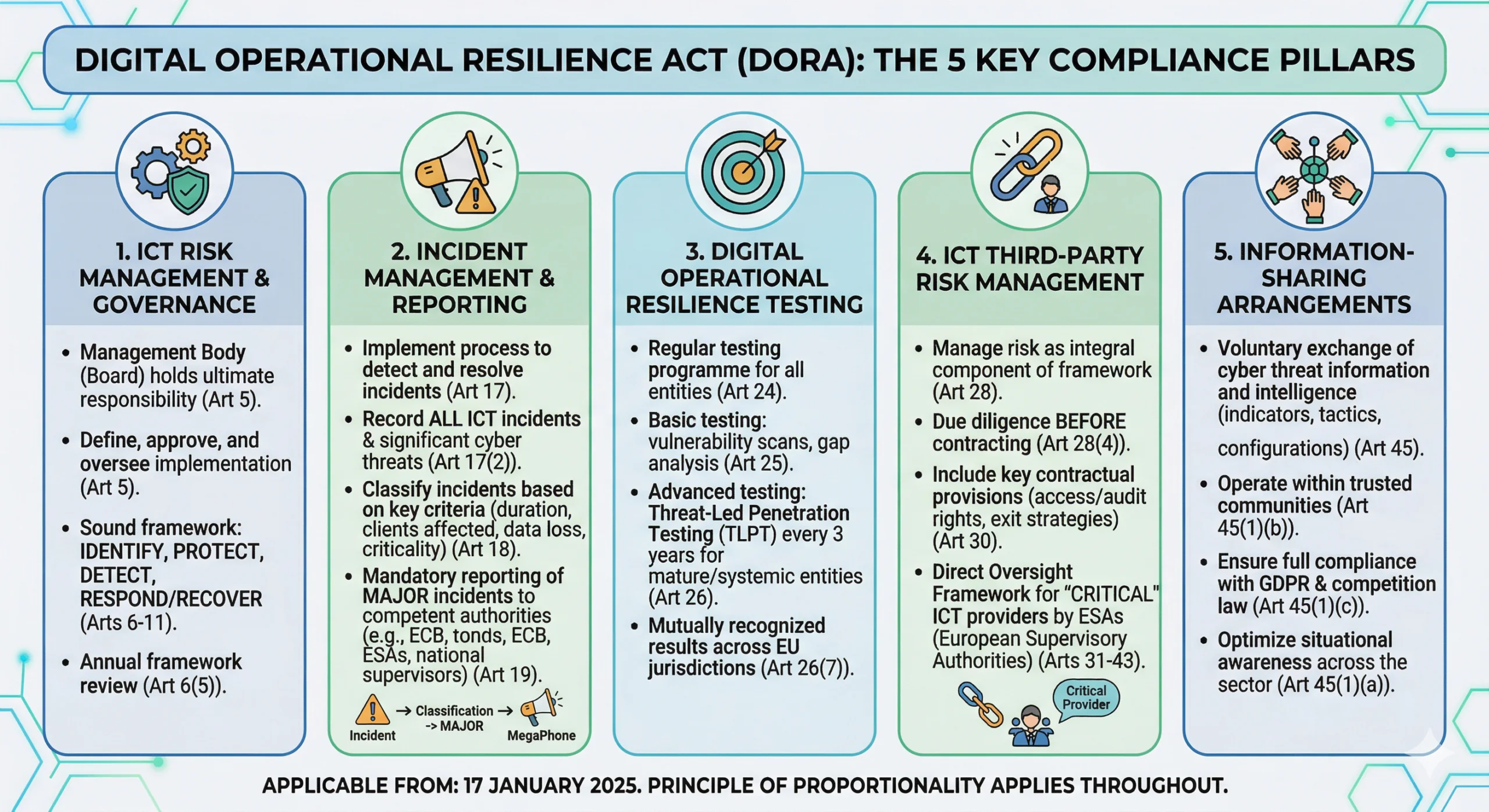
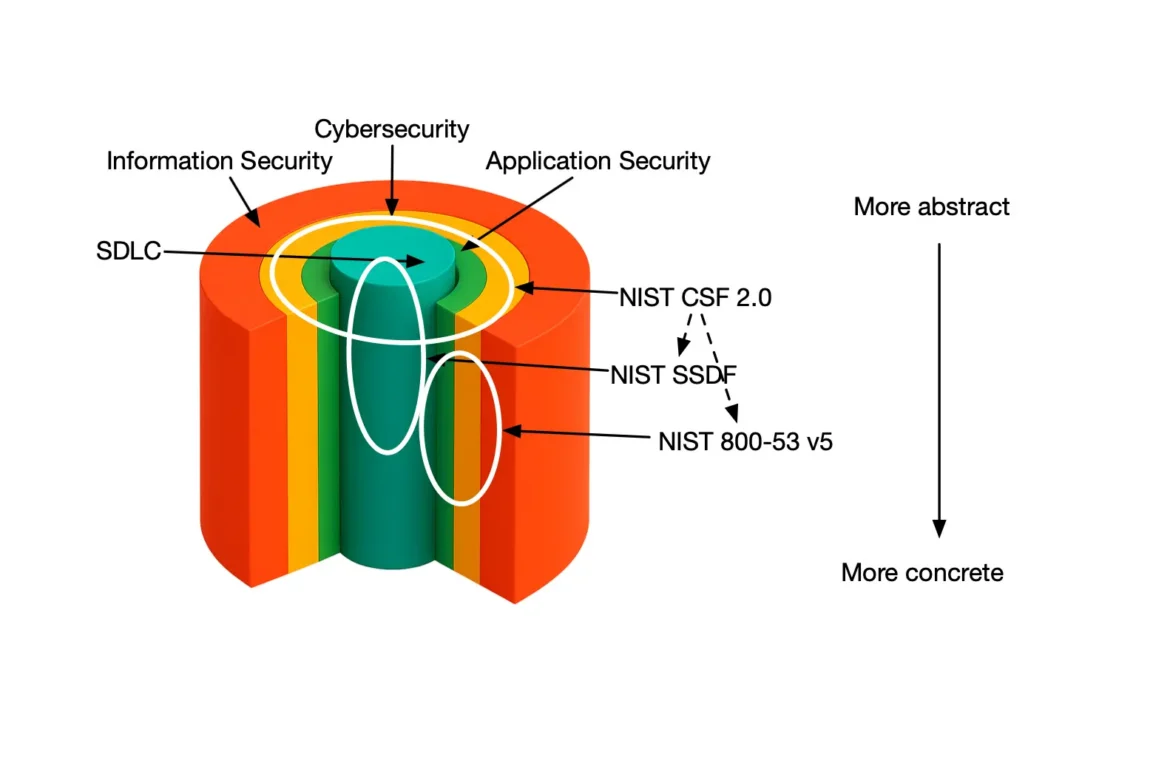
Pillar I: ICT Risk Management
At the heart of DORA is the requirement for a “sound, comprehensive and well-documented” ICT risk management framework. This framework must be an integral part of the entity’s overall risk management system.
Governance and Accountability
The management body (the Board) can no longer delegate technology risk into oblivion. Under DORA, the Board:
- Bears ultimate responsibility for managing ICT risk.
- Must approve and periodically review the digital operational resilience strategy.
- Must allocate appropriate budgets for ICT security and training.
- Must stay updated with “sufficient knowledge and skills” to understand ICT risk through regular training.
The Lifecycle of Risk Management
The framework requires entities to:
- Identify: Map all business functions and the ICT assets supporting them, including “legacy ICT systems”.
- Protect and Prevent: Implement security tools like strong authentication, encryption, and patch management policies.
- Detect: Deploy mechanisms to promptly find anomalous activities and potential single points of failure.
- Respond and Recover: Maintain comprehensive business continuity plans that allow for the “timely restoration of services” after an incident.
Pillar II: Incident Management & Reporting
DORA aims to eliminate the “administrative burden” of duplicative reporting. Financial entities must now follow a streamlined process to detect, manage, and notify the authorities of ICT-related incidents.
Classification of Incidents
Not every glitch requires a report to the regulator. Entities must classify incidents based on criteria like the number of clients affected, duration, geographical spread, and data loss. Only major ICT-related incidents must be reported.
The Reporting Timeline
When a major incident occurs, entities must submit:
- An initial notification.
- An intermediate report when the status changes significantly.
- A final report once the root cause analysis is complete.
Pillar III: Digital Operational Resilience Testing
To ensure their defenses aren’t just paper-thin, entities must establish a testing programme. This includes basic assessments like vulnerability scans, open-source analyses, and network security reviews.
Advanced Testing (TLPT)
For significant and “ICT-mature” entities, DORA mandates Threat-Led Penetration Testing (TLPT) at least every three years. TLPT mimics the tactics of real-life threat actors to test “live production systems”.
- Testers: Can be internal or external, but external testers must be used every three tests to ensure objectivity.
- Scope: Must cover critical or important functions and include any relevant ICT third-party service providers.
Pillar IV: Managing Third-Party Risk
One of DORA’s most innovative features is the Oversight Framework for critical ICT third-party service providers. Recognizing that a failure at a major cloud provider could cripple the entire financial system, the EU has introduced direct oversight of “Big Tech”.
Key Contractual Provisions
Contracts between financial entities and ICT providers must be “resolution resilient” and include:
- Full service level descriptions with precise performance targets.
- Locations where data is processed.
- Unrestricted rights of access, inspection, and audit.
- Dedicated exit strategies to allow the migration to another provider without business disruption.
The Oversight of “Critical” Providers
The European Supervisory Authorities (ESAs) will designate certain providers as critical. These providers will be assigned a Lead Overseer who has the power to:
- Conduct on-site inspections.
- Issue recommendations to address ICT risks.
- Impose periodic penalty payments of up to 1% of the average daily worldwide turnover to compel compliance.
Information Sharing and Cooperation
DORA encourages the “regular sharing” of threat intelligence. Financial entities can set up arrangements to exchange indicators of compromise, tactics, and cyber security alerts. This collective defense mechanism must be conducted within “trusted communities” and in full compliance with GDPR and competition laws.
Supervision and Enforcement
Compliance is monitored by national competent authorities (such as the ECB for significant banks). These authorities have “supervisory, investigatory and sanctioning powers,” including the ability to:
- Access any relevant document or data.
- Issue orders to cease conduct that breaches the Regulation.
- Publish notices identifying the person responsible for a breach.
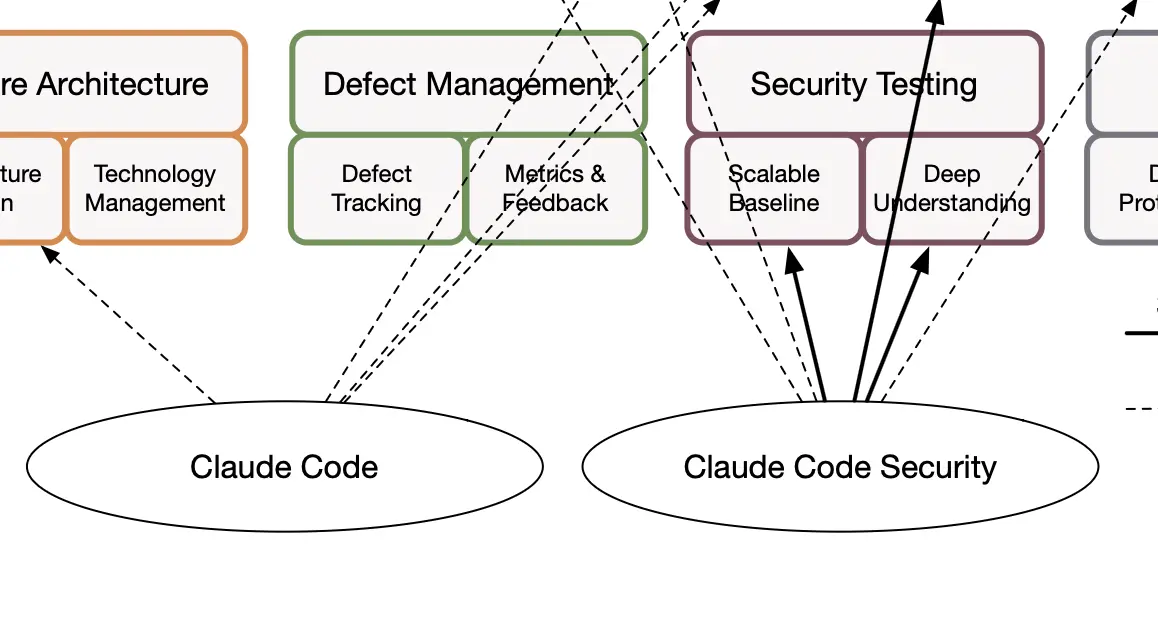
Stay on top of all your obligations with SAMMY
We created SAMMY to help organizations inventorize their security practices and use different frameworks to get visibility on maturity and compliance. Find out more on SAMMY.codific.com.