Your Guide to OWASP SAMM: Insights and Best Practices
The OWASP Software Assurance Maturity Model (SAMM) is a powerful tool for improving software security practices. It provides clear steps and a structured approach, enabling teams to assess their current security posture and build better strategies. Our OWASP SAMM Guidance page is here to help you make the most of this framework. It includes practical tips, expert advice, and useful resources to guide you through implementing OWASP SAMM in your organization.
Security verification with Jmeter Stress Test
Updated: 4 April, 2025 5 September, 2022 Security verification is about validating that a system or application adheres to predefined security requirements or standards. There are many types of security verification activities ranging from penetration testing to vulnerability scans by automated tools. One of the less known types of security verification is the stress testing. Stress testing is part of what Software Assurance Maturity Model (SAMM) calls “misuse/abuse testing”. Misuse/Abuse testing aims to detect unexpected design flaws and implementation bugs by focusing on the so-called negative tests trying to “break” something in the system. Wait, but isn’t stress testing mainly related to testing the scalability of the system? Well, it is! However availability is one of the core security qualities, alongside confidentiality and integrity. Hence, stress testing is an inherent part of security verification testing. In this blog we present our insights in implementing stress testing at Codific. We also […]
OWASP SAMM: Education and Guidance
Updated: 9 March, 2026 9 June, 2022 Ever heard the saying “our team is our greatest asset”. I’d dare to say that this is rule number 1 through 10 if you are running a company. Any company! Well, except for a one-man show (where this is self-explanatory and you don’t really need a rule)! Thus security training and organizational culture are the pillars of your SDLC programme. Unless you are just trying to check the boxes this security practice should get the highest priority in your SAMM implementation roadmap. In this blog series, we present how Codific implements OWASP SAMM. In each blog we focus on a specific security practice and highlight the processes and tools we use to achieve a certain maturity level. If you would like to learn more about OWASP SAMM, take our free SAMM training. My journey in application security (AppSec) started almost 20 years ago[…]
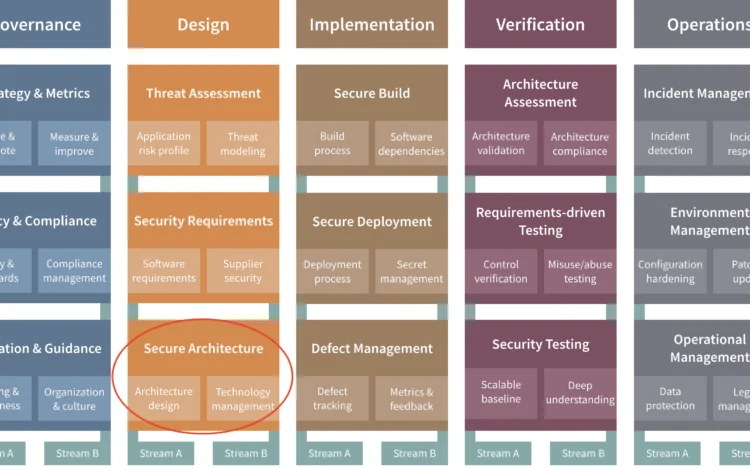
OWASP SAMM: Secure Architecture
Updated: 1 October, 2025 24 May, 2022 Secure architecture in a nutshell In application security, architecture is of paramount importance. The secure architecture practice focuses on security during the architectural design of the software system. It is the practice of application security architecture in OWASP SAMM. The essence of this practice is to leverage proven patterns and principles both in terms of an architectural solution as well as technological implementation. On top of that you should ideally revisit the reference solutions, update them and propagate the changes back to your software systems in production. This practice is an essential step in claiming the security by design principle. In this blog series, we present how Codific implements OWASP SAMM. Obviously describing all details is out of scope especially for this practice. We will however present a high-level overview and describe some of the tools we leverage to achieve a specific maturity[…]
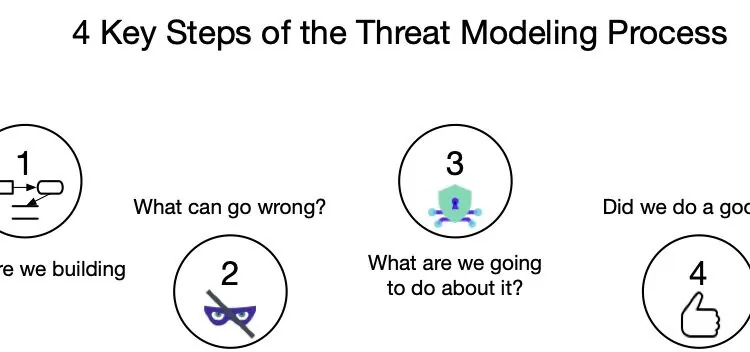
OWASP SAMM: Pragmatic Threat Modeling Best Practices
Updated: 9 March, 2026 26 April, 2022 Threat modeling yields the highest return on investment when it comes to your Application Security program. Even if your current security posture is close to a zero OWASP SAMM score, you should start by threat modeling first. As opposed to what many might think, threat modeling is not difficult nor time-consuming. It is by far the most underrated security practice out there. Intro In this blog series, we will present how Codific implements OWASP SAMM. We focus on a specific security practice in each blog and highlight the processes and tools we use to achieve a certain maturity level. If you want to learn more about OWASP SAMM consider taking the free SAMM training. Extract from the OWASP SAMM Fundamentals training. My journey in application security (AppSec) started almost 20 years ago at the DistriNet research lab of the University of Leuven. Back[…]
Why Choose OWASP SAMM?
Using OWASP SAMM can help you pinpoint weak spots in your software development process and uncover actionable ways to improve. This framework is structured to assess your current practices, provide clear benchmarks, and guide you toward a more secure development lifecycle. Furthermore, whether you’re just starting with OWASP SAMM or aiming to refine your existing approach, our OWASP SAMM Guidance delivers the tools and insights you need to succeed.
Unlock Additional Resources
Our guidance connects you to a wealth of additional resources. For example, these include best practices for secure design, development, and deployment. Moreover, internal links throughout this page will direct you to case studies, practical tips, and related articles. By exploring these, you can expand your knowledge and implement improvements step by step.
How SAMMY Supports OWASP SAMM
By focusing on OWASP SAMM Guidance, your team can build stronger, more secure software. Additionally, this framework works seamlessly with SAMMY, our innovative security software. SAMMY integrates OWASP SAMM principles to simplify security assessments and streamline the improvement process. Therefore, for organizations aiming to boost their security quickly and effectively, SAMMY is an invaluable tool.
Take the Next Step
Start your journey today and discover how OWASP SAMM and SAMMY can transform your development processes. With the right tools and guidance, you can ensure your software meets the highest security standards. Furthermore, dive into our related content to explore practical steps for integrating SAMMY into your OWASP SAMM journey. Together, these frameworks empower you to protect your software and strengthen your security posture.